Pentester Academy - Web Application Pentesting & Javascript for Pentesters
MP4 | AVC 1246kbps | English | 1280x1024 | 30fps | AAC stereo 242kbps | 6.23 GB
Genre: Video Training
In this course, we will be learning how to use Javascript for Pentesting.
A non-exhaustive and continuously evolving list of topics to be covered include:
HTTP/HTTPS protocol basics
Understanding Web Application Architectures
Lab setup and tools of the trade
Converting your browser into an attack platform
Traffic Interception and Modification using Proxies
Cross Site Scripting
Types
Reflected
Persistent
DOM based
Filtering XSS
Evading XSS filters
Cookie stealing and session hijacking
Self-XSS
BeeF
SQL Injection
Error based
Blind
Second order injections
Broken authentication and session management
session id analysis
custom authentication
Security misconfigurations
Web and database server
Application framework
Insecure direct object reference
Cross-site Request Forgery
GET and POST based
JSON based in RESTful Service
Token Hijacking via XSS
Multi-Step CSRF
Insecure cryptographic storage
Clickjacking
File upload vulnerabilities
Bypassing extension, content-type etc. checks
RFI and LFI
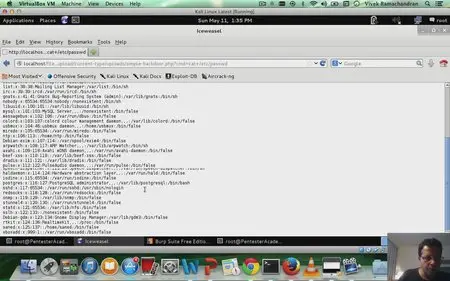
Web to Shell
Web Shells
PHP meterpreter
Analyzing Web 2.0 applications
AJAX
RIAs using Flash, Flex
Attacking Caching servers
Memcached
Redis
Non Relational Database Attacks
Appengine Datastore
MongoDB, CouchDB etc.
HTML5 Attack Vectors
Tag abuse and use in XSS
Websockets
Client side injection
Clickjacking
Web Application firewalls
Fingerprinting
Detection Techniques
Evading WAFs
… more additions will be made as course evolves
Task 1: Modify HTML with Javascript
2 Task 1 Solution: Modify HTML with Javascript
Task 1 Solution: Modify HTML with Javascript
3 Task 2: Change All Links
Task 2: Change All Links
4 Task 2 Solution: Change All Links
Task 2 Solution: Change All Links
5 Task 3: Hijack Form Submit
Task 3: Hijack Form Submit
6 Task 3 Solution: Hijack Form Submit
Task 3 Solution: Hijack Form Submit
7 Task 4: Modify Form Fields
Task 4: Modify Form Fields
8 Task 4 Solution: Modify Form Fields
Task 4 Solution: Modify Form Fields
9 Task 5: Social Engineering
Task 5: Social Engineering
10 Task 5 Solution: Social Engineering
Task 5 Solution: Social Engineering
11 Task 6: Capture All Clicks
Task 6: Capture All Clicks
12 Task 6 Solution: Capture All Clicks
Task 6 Solution: Capture All Clicks
13 Task 7: Keystroke Logging
Task 7: Keystroke Logging
14 Task 7 Solution: Keystroke Logging
Task 7 Solution: Keystroke Logging
15 Task 8: Event Listener
Task 8: Event Listener
16 Task 8 Solution: Event Listener
Task 8 Solution: Event Listener
17 Task 9: Include External JS
Task 9: Include External JS
18 Task 10: Include External JS using JS
Task 10: Include External JS using JS
19 Task 11: Replace Banner Image
Task 11: Replace Banner Image
20 Task 12: Stealing from Auto-Complete
Task 12: Stealing from Auto-Complete
21 Task 13: Posting with XMLHttpRequest
Task 13: Posting with XMLHttpRequest
22 Task 14: Fetching Data with XMLHttpRequest
Task 14: Fetching Data with XMLHttpRequest
23 Task 15: Data Exfiltration with XMLHttpRequest
Task 15: Data Exfiltration with XMLHttpRequest
24 Task 9 Solution: Include External JS
Task 9 Solution: Include External JS
25 Task 10 Solution: Include External JS using JS
Task 10 Solution: Include External JS using JS
26 Task 11 Solution: Replace Banner Image
Task 11 Solution: Replace Banner Image
27 Task 12 Solution: Stealing from Auto-Complete
Task 12 Solution: Stealing from Auto-Complete
28 Task 13 Solution: Posting with XMLHttpRequest
Task 13 Solution: Posting with XMLHttpRequest
29 Task 14 Solution: Fetching Data with XMLHttpRequest
Task 14 Solution: Fetching Data with XMLHttpRequest
30 Task 15 Solution: Data Exfiltration with XMLHttpRequest
Task 15 Solution: Data Exfiltration with XMLHttpRequest
31 Task 16: Extracting CSRF Tokens
Task 16: Extracting CSRF Tokens
32 Task 17: CSRF Token Stealing
Task 17: CSRF Token Stealing
33 Task 18: HTML Parsing of XMLHttpRequest Response
Task 18: HTML Parsing of XMLHttpRequest Response
34 Task 16 Solution: Extracting CSRF Tokens
Task 16 Solution: Extracting CSRF Tokens
35 Task 17 Solution: CSRF Token Stealing
Task 17 Solution: CSRF Token Stealing
36 Task 18 Solution: HTML Parsing of XMLHttpRequest Response
Task 18 Solution: HTML Parsing of XMLHttpRequest Response
37 Task 19: Multi-Level HTML Parsing
Task 19: Multi-Level HTML Parsing
38 Task 20: Multi-Level JSON Parsing
Task 20: Multi-Level JSON Parsing
39 Task 21: Multi-Level XML Parsing
Task 21: Multi-Level XML Parsing
40 Task 19 Solution: Multi-Level HTML Parsing
Task 19 Solution: Multi-Level HTML Parsing
41 Task 20 Solution: Multi-Level JSON Parsing
Task 20 Solution: Multi-Level JSON Parsing
42 Task 21 Solution: Multi-Level XML Parsing
Task 21 Solution: Multi-Level XML Parsing
Course Introduction
2 HTTP Basics
HTTP Basics
3 Netcat Lab for HTTP 1.1 and 1.0
Netcat Lab for HTTP 1.1 and 1.0
4 HTTP Methods and Verb Tampering
HTTP Methods and Verb Tampering
5 HTTP Method Testing with Nmap and Metasploit
HTTP Method Testing with Nmap and Metasploit
6 HTTP Verb Tampering Demo
HTTP Verb Tampering Demo
7 HTTP Verb Tampering Lab Exercise
HTTP Verb Tampering Lab Exercise
8 HTTP Basic Authentication
HTTP Basic Authentication
9 Attacking HTTP Basic Authentication with Nmap and Metasploit
Attacking HTTP Basic Authentication with Nmap and Metasploit
10 HTTP Digest Authentication RFC 2069
HTTP Digest Authentication RFC 2069
11 HTTP Digest Auth Hashing (RFC 2069)
HTTP Digest Auth Hashing (RFC 2069)
12 HTTP Digest Authentication (RFC 2617)
HTTP Digest Authentication (RFC 2617)
13 HTTP Statelessness and Cookies
HTTP Statelessness and Cookies
14 HTTP Set-Cookie with HTTPCookie
HTTP Set-Cookie with HTTPCookie
15 Session ID
Session ID
16 SSL - Transport Layer Protection
SSL - Transport Layer Protection
17 SSL MITM using Proxies
SSL MITM using Proxies
18 File Extraction from HTTP Traffic
File Extraction from HTTP Traffic
19 HTML Injection Basics
HTML Injection Basics
20 HTML Injection in Tag Parameters
HTML Injection in Tag Parameters
21 HTML Injection using 3rd Party Data Source
HTML Injection using 3rd Party Data Source
22 HTML Injection - Bypass Filters Cgi.Escape
HTML Injection - Bypass Filters Cgi.Escape
23 Command Injection
Command Injection
24 Command Injection - Filters
Command Injection - Filters
25 Web to Shell on the Server
Web to Shell on the Server
26 Web Shell: PHP Meterpreter
Web Shell: PHP Meterpreter
27 Web Shell: Netcat Reverse Connects
Web Shell: Netcat Reverse Connects
28 Web Shell: Using Python, PHP etc.
Web Shell: Using Python, PHP etc.
29 Getting Beyond Alert(XSS)
Getting Beyond Alert(XSS)
30 Javascript for Pentesters: Introduction and Hello World
Javascript for Pentesters: Introduction and Hello World
31 XSS: Cross Site Scripting
XSS: Cross Site Scripting
32 Javascript for Pentesters: Variables
Javascript for Pentesters: Variables
33 Types of XSS
Types of XSS
34 Javascript for Pentesters: Operators
Javascript for Pentesters: Operators
35 XSS via Event Handler Attributes
XSS via Event Handler Attributes
36 Javascript for Pentesters: Conditionals
Javascript for Pentesters: Conditionals
37 DOM XSS
DOM XSS
38 Javascript for Pentesters: Loops
Javascript for Pentesters: Loops
39 Javascript for Pentesters: Functions
Javascript for Pentesters: Functions
40 Javascript for Pentesters: Data Types
Javascript for Pentesters: Data Types
41 Javascript for Pentesters: Enumerating Object Properties
Javascript for Pentesters: Enumerating Object Properties
42 Javascript for Pentesters: HTML DOM
Javascript for Pentesters: HTML DOM
43 Javascript for Pentesters: Event Handlers
Javascript for Pentesters: Event Handlers
44 Javascript for Pentesters: Cookies
Javascript for Pentesters: Cookies
45 Javascript for Pentesters: Stealing Cookies
Javascript for Pentesters: Stealing Cookies
46 Javascript for Pentesters: Exceptions
Javascript for Pentesters: Exceptions
47 Javascript for Pentesters: Advanced Forms Manipulation
Javascript for Pentesters: Advanced Forms Manipulation
48 Javascript for Pentesters: XMLHttpRequest Basics
Javascript for Pentesters: XMLHttpRequest Basics
49 Javascript for Pentesters: XHR and HTML Parsing
Javascript for Pentesters: XHR and HTML Parsing
50 Javascript for Pentesters: XHR and JSON Parsing
Javascript for Pentesters: XHR and JSON Parsing
51 Javascript for Pentesters: XHR and XML Parsing
Javascript for Pentesters: XHR and XML Parsing
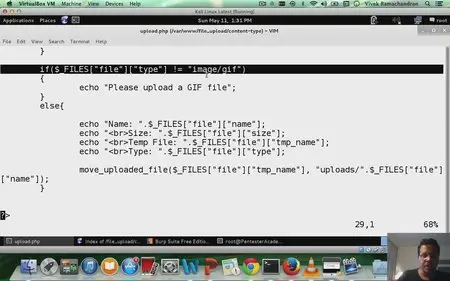
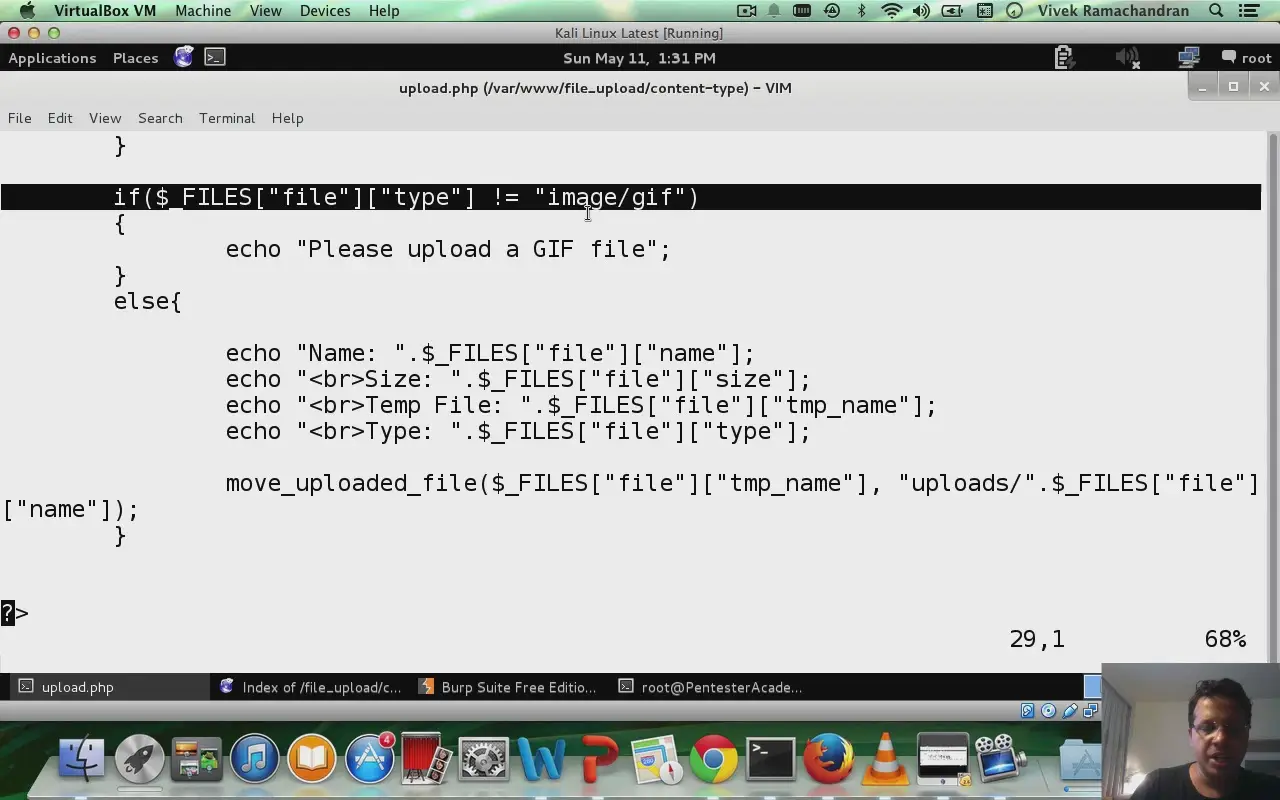
52 File Upload Vulnerability Basics
File Upload Vulnerability Basics
53 Beating Content-Type Check in File Uploads
Beating Content-Type Check in File Uploads
54 Bypassing Blacklists in File Upload
Bypassing Blacklists in File Upload
55 Bypassing Blacklists using PHPx
Bypassing Blacklists using PHPx
56 Bypassing Whitelists using Double Extensions in File Uploads
Bypassing Whitelists using Double Extensions in File Uploads
57 Defeating Getimagesize() Checks in File Uploads
Defeating Getimagesize() Checks in File Uploads
58 Null Byte Injection in File Uploads
Null Byte Injection in File Uploads
59 Exploiting File Uploads to get Meterpreter
Exploiting File Uploads to get Meterpreter
60 Remote File Inclusion Vulnerability Basics
Remote File Inclusion Vulnerability Basics
61 Exploiting RFI with Forced Extensions
Exploiting RFI with Forced Extensions
62 RFI to Meterpreter
RFI to Meterpreter
63 LFI Basics
LFI Basics
64 LFI with Directory Prepends
LFI with Directory Prepends
65 Remote Code Execution with LFI and File Upload Vulnerability
Remote Code Execution with LFI and File Upload Vulnerability
66 LFI with File Extension Appended - Null Byte Injection�
LFI with File Extension Appended - Null Byte Injection
67 Remote Code Execution with LFI and Apache Log Poisoning
Remote Code Execution with LFI and Apache Log Poisoning
68 Remote Code Execution with LFI and SSH Log Poisoning
Remote Code Execution with LFI and SSH Log Poisoning
69 Unvalidated Redirects
Unvalidated Redirects
70 Encoding Redirect Params
Encoding Redirect Params
71 Open Redirects: Base64 Encoded Params
Open Redirects: Base64 Encoded Params
72 Open Redirects: Beating Hash Checking
Open Redirects: Beating Hash Checking
73 Open Redirects: Hashing with Salt
Open Redirects: Hashing with Salt
74 Securing Open Redirects
Securing Open Redirects
75 Cross Site Request Forgery Basics
Cross Site Request Forgery Basics
76 Cross Site Request Forgery Trigger Tags
Cross Site Request Forgery Trigger Tags
77 CSRF Multi-Step Operation Handling
CSRF Multi-Step Operation Handling
78 Mitigating CSRF with Tokens
Mitigating CSRF with Tokens
79 CSRF and XSS
CSRF and XSS
80 CSRF Token Bypass with Hidden Iframes
CSRF Token Bypass with Hidden Iframes
81 Insecure Direct Object Reference
Insecure Direct Object Reference
82 Insecure Direct Object Reference (Burp Demo)
Insecure Direct Object Reference (Burp Demo)
2 Task 1 Solution: Modify HTML with Javascript
Task 1 Solution: Modify HTML with Javascript
3 Task 2: Change All Links
Task 2: Change All Links
4 Task 2 Solution: Change All Links
Task 2 Solution: Change All Links
5 Task 3: Hijack Form Submit
Task 3: Hijack Form Submit
6 Task 3 Solution: Hijack Form Submit
Task 3 Solution: Hijack Form Submit
7 Task 4: Modify Form Fields
Task 4: Modify Form Fields
8 Task 4 Solution: Modify Form Fields
Task 4 Solution: Modify Form Fields
9 Task 5: Social Engineering
Task 5: Social Engineering
10 Task 5 Solution: Social Engineering
Task 5 Solution: Social Engineering
11 Task 6: Capture All Clicks
Task 6: Capture All Clicks
12 Task 6 Solution: Capture All Clicks
Task 6 Solution: Capture All Clicks
13 Task 7: Keystroke Logging
Task 7: Keystroke Logging
14 Task 7 Solution: Keystroke Logging
Task 7 Solution: Keystroke Logging
15 Task 8: Event Listener
Task 8: Event Listener
16 Task 8 Solution: Event Listener
Task 8 Solution: Event Listener
17 Task 9: Include External JS
Task 9: Include External JS
18 Task 10: Include External JS using JS
Task 10: Include External JS using JS
19 Task 11: Replace Banner Image
Task 11: Replace Banner Image
20 Task 12: Stealing from Auto-Complete
Task 12: Stealing from Auto-Complete
21 Task 13: Posting with XMLHttpRequest
Task 13: Posting with XMLHttpRequest
22 Task 14: Fetching Data with XMLHttpRequest
Task 14: Fetching Data with XMLHttpRequest
23 Task 15: Data Exfiltration with XMLHttpRequest
Task 15: Data Exfiltration with XMLHttpRequest
24 Task 9 Solution: Include External JS
Task 9 Solution: Include External JS
25 Task 10 Solution: Include External JS using JS
Task 10 Solution: Include External JS using JS
26 Task 11 Solution: Replace Banner Image
Task 11 Solution: Replace Banner Image
27 Task 12 Solution: Stealing from Auto-Complete
Task 12 Solution: Stealing from Auto-Complete
28 Task 13 Solution: Posting with XMLHttpRequest
Task 13 Solution: Posting with XMLHttpRequest
29 Task 14 Solution: Fetching Data with XMLHttpRequest
Task 14 Solution: Fetching Data with XMLHttpRequest
30 Task 15 Solution: Data Exfiltration with XMLHttpRequest
Task 15 Solution: Data Exfiltration with XMLHttpRequest
31 Task 16: Extracting CSRF Tokens
Task 16: Extracting CSRF Tokens
32 Task 17: CSRF Token Stealing
Task 17: CSRF Token Stealing
33 Task 18: HTML Parsing of XMLHttpRequest Response
Task 18: HTML Parsing of XMLHttpRequest Response
34 Task 16 Solution: Extracting CSRF Tokens
Task 16 Solution: Extracting CSRF Tokens
35 Task 17 Solution: CSRF Token Stealing
Task 17 Solution: CSRF Token Stealing
36 Task 18 Solution: HTML Parsing of XMLHttpRequest Response
Task 18 Solution: HTML Parsing of XMLHttpRequest Response
37 Task 19: Multi-Level HTML Parsing
Task 19: Multi-Level HTML Parsing
38 Task 20: Multi-Level JSON Parsing
Task 20: Multi-Level JSON Parsing
39 Task 21: Multi-Level XML Parsing
Task 21: Multi-Level XML Parsing
40 Task 19 Solution: Multi-Level HTML Parsing
Task 19 Solution: Multi-Level HTML Parsing
41 Task 20 Solution: Multi-Level JSON Parsing
Task 20 Solution: Multi-Level JSON Parsing
42 Task 21 Solution: Multi-Level XML Parsing
Task 21 Solution: Multi-Level XML Parsing
Course Introduction
2 HTTP Basics
HTTP Basics
3 Netcat Lab for HTTP 1.1 and 1.0
Netcat Lab for HTTP 1.1 and 1.0
4 HTTP Methods and Verb Tampering
HTTP Methods and Verb Tampering
5 HTTP Method Testing with Nmap and Metasploit
HTTP Method Testing with Nmap and Metasploit
6 HTTP Verb Tampering Demo
HTTP Verb Tampering Demo
7 HTTP Verb Tampering Lab Exercise
HTTP Verb Tampering Lab Exercise
8 HTTP Basic Authentication
HTTP Basic Authentication
9 Attacking HTTP Basic Authentication with Nmap and Metasploit
Attacking HTTP Basic Authentication with Nmap and Metasploit
10 HTTP Digest Authentication RFC 2069
HTTP Digest Authentication RFC 2069
11 HTTP Digest Auth Hashing (RFC 2069)
HTTP Digest Auth Hashing (RFC 2069)
12 HTTP Digest Authentication (RFC 2617)
HTTP Digest Authentication (RFC 2617)
13 HTTP Statelessness and Cookies
HTTP Statelessness and Cookies
14 HTTP Set-Cookie with HTTPCookie
HTTP Set-Cookie with HTTPCookie
15 Session ID
Session ID
16 SSL - Transport Layer Protection
SSL - Transport Layer Protection
17 SSL MITM using Proxies
SSL MITM using Proxies
18 File Extraction from HTTP Traffic
File Extraction from HTTP Traffic
19 HTML Injection Basics
HTML Injection Basics
20 HTML Injection in Tag Parameters
HTML Injection in Tag Parameters
21 HTML Injection using 3rd Party Data Source
HTML Injection using 3rd Party Data Source
22 HTML Injection - Bypass Filters Cgi.Escape
HTML Injection - Bypass Filters Cgi.Escape
23 Command Injection
Command Injection
24 Command Injection - Filters
Command Injection - Filters
25 Web to Shell on the Server
Web to Shell on the Server
26 Web Shell: PHP Meterpreter
Web Shell: PHP Meterpreter
27 Web Shell: Netcat Reverse Connects
Web Shell: Netcat Reverse Connects
28 Web Shell: Using Python, PHP etc.
Web Shell: Using Python, PHP etc.
29 Getting Beyond Alert(XSS)
Getting Beyond Alert(XSS)
30 Javascript for Pentesters: Introduction and Hello World
Javascript for Pentesters: Introduction and Hello World
31 XSS: Cross Site Scripting
XSS: Cross Site Scripting
32 Javascript for Pentesters: Variables
Javascript for Pentesters: Variables
33 Types of XSS
Types of XSS
34 Javascript for Pentesters: Operators
Javascript for Pentesters: Operators
35 XSS via Event Handler Attributes
XSS via Event Handler Attributes
36 Javascript for Pentesters: Conditionals
Javascript for Pentesters: Conditionals
37 DOM XSS
DOM XSS
38 Javascript for Pentesters: Loops
Javascript for Pentesters: Loops
39 Javascript for Pentesters: Functions
Javascript for Pentesters: Functions
40 Javascript for Pentesters: Data Types
Javascript for Pentesters: Data Types
41 Javascript for Pentesters: Enumerating Object Properties
Javascript for Pentesters: Enumerating Object Properties
42 Javascript for Pentesters: HTML DOM
Javascript for Pentesters: HTML DOM
43 Javascript for Pentesters: Event Handlers
Javascript for Pentesters: Event Handlers
44 Javascript for Pentesters: Cookies
Javascript for Pentesters: Cookies
45 Javascript for Pentesters: Stealing Cookies
Javascript for Pentesters: Stealing Cookies
46 Javascript for Pentesters: Exceptions
Javascript for Pentesters: Exceptions
47 Javascript for Pentesters: Advanced Forms Manipulation
Javascript for Pentesters: Advanced Forms Manipulation
48 Javascript for Pentesters: XMLHttpRequest Basics
Javascript for Pentesters: XMLHttpRequest Basics
49 Javascript for Pentesters: XHR and HTML Parsing
Javascript for Pentesters: XHR and HTML Parsing
50 Javascript for Pentesters: XHR and JSON Parsing
Javascript for Pentesters: XHR and JSON Parsing
51 Javascript for Pentesters: XHR and XML Parsing
Javascript for Pentesters: XHR and XML Parsing
52 File Upload Vulnerability Basics
File Upload Vulnerability Basics
53 Beating Content-Type Check in File Uploads
Beating Content-Type Check in File Uploads
54 Bypassing Blacklists in File Upload
Bypassing Blacklists in File Upload
55 Bypassing Blacklists using PHPx
Bypassing Blacklists using PHPx
56 Bypassing Whitelists using Double Extensions in File Uploads
Bypassing Whitelists using Double Extensions in File Uploads
57 Defeating Getimagesize() Checks in File Uploads
Defeating Getimagesize() Checks in File Uploads
58 Null Byte Injection in File Uploads
Null Byte Injection in File Uploads
59 Exploiting File Uploads to get Meterpreter
Exploiting File Uploads to get Meterpreter
60 Remote File Inclusion Vulnerability Basics
Remote File Inclusion Vulnerability Basics
61 Exploiting RFI with Forced Extensions
Exploiting RFI with Forced Extensions
62 RFI to Meterpreter
RFI to Meterpreter
63 LFI Basics
LFI Basics
64 LFI with Directory Prepends
LFI with Directory Prepends
65 Remote Code Execution with LFI and File Upload Vulnerability
Remote Code Execution with LFI and File Upload Vulnerability
66 LFI with File Extension Appended - Null Byte Injection�
LFI with File Extension Appended - Null Byte Injection
67 Remote Code Execution with LFI and Apache Log Poisoning
Remote Code Execution with LFI and Apache Log Poisoning
68 Remote Code Execution with LFI and SSH Log Poisoning
Remote Code Execution with LFI and SSH Log Poisoning
69 Unvalidated Redirects
Unvalidated Redirects
70 Encoding Redirect Params
Encoding Redirect Params
71 Open Redirects: Base64 Encoded Params
Open Redirects: Base64 Encoded Params
72 Open Redirects: Beating Hash Checking
Open Redirects: Beating Hash Checking
73 Open Redirects: Hashing with Salt
Open Redirects: Hashing with Salt
74 Securing Open Redirects
Securing Open Redirects
75 Cross Site Request Forgery Basics
Cross Site Request Forgery Basics
76 Cross Site Request Forgery Trigger Tags
Cross Site Request Forgery Trigger Tags
77 CSRF Multi-Step Operation Handling
CSRF Multi-Step Operation Handling
78 Mitigating CSRF with Tokens
Mitigating CSRF with Tokens
79 CSRF and XSS
CSRF and XSS
80 CSRF Token Bypass with Hidden Iframes
CSRF Token Bypass with Hidden Iframes
81 Insecure Direct Object Reference
Insecure Direct Object Reference
82 Insecure Direct Object Reference (Burp Demo)
Insecure Direct Object Reference (Burp Demo)
No mirrors please